1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
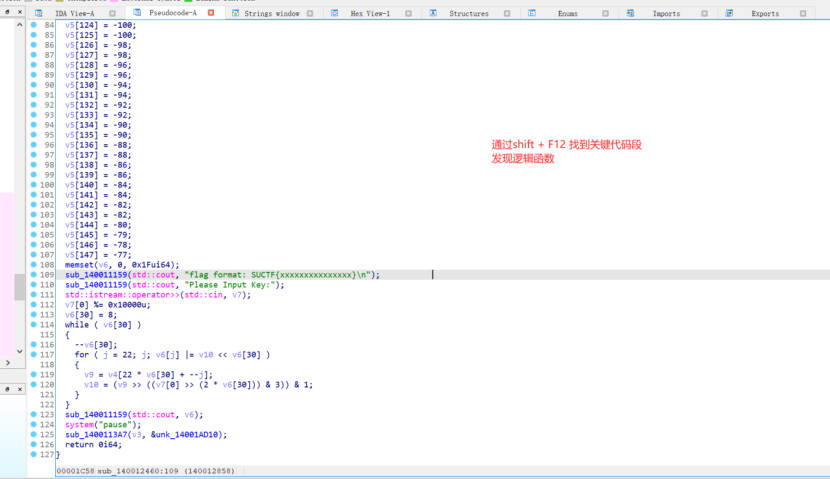
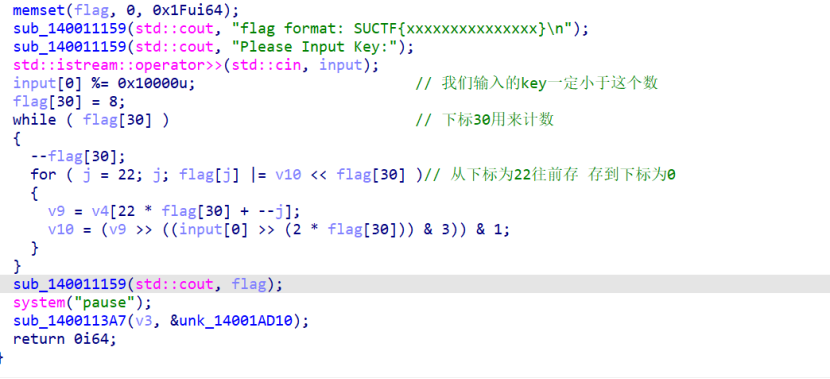
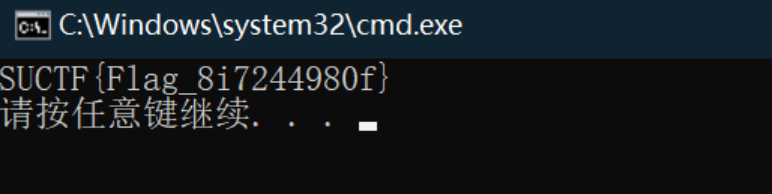
| #include <stdio.h>
int main(void)
{
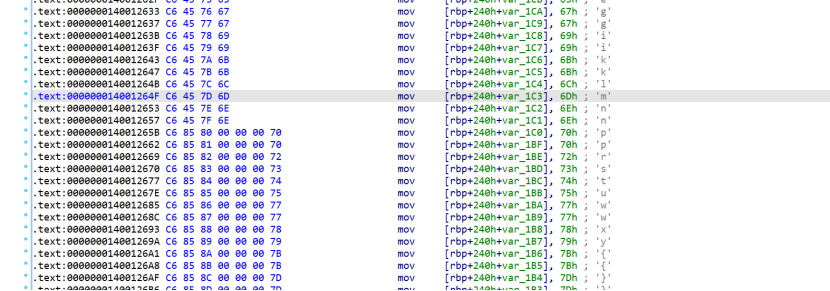
unsigned char data[] =
{
0x2, 0x3, 0x2, 0x1, 0x4, 0x7, 0x4, 0x5, 0xA, 0xB, 0xA, 0x9, 0xE, 0xF, 0xC, 0xD, 0x10, 0x13, 0x10, 0x11, 0x14, 0x17, 0x16, 0x13, 0x1C, 0x19, 0x1E, 0x1F, 0x1C, 0x19, 0x1A, 0x1F, 0x24, 0x21, 0x22, 0x27, 0x24, 0x21, 0x22, 0x23, 0x28, 0x29, 0x2E, 0x2B, 0x24, 0x2D, 0x26, 0x2F, 0x38, 0x31, 0x3A, 0x3B, 0x34, 0x3D, 0x3E, 0x37, 0x30, 0x39, 0x32, 0x3B, 0x3C, 0x35, 0x36, 0x37, 0x48, 0x49, 0x42, 0x42, 0x44, 0x44, 0x46, 0x47, 0x48, 0x49, 0x4A, 0x4A, 0x4D, 0x4D, 0x4F, 0x4E, 0x50, 0x50, 0x52, 0x53, 0x55, 0x54, 0x56, 0x57, 0x59, 0x59, 0x5A, 0x5B, 0x5C, 0x5D, 0x5E, 0x5E, 0x60, 0x60, 0x63, 0x63, 0x64, 0x65, 0x67, 0x67, 0x69, 0x69, 0x6B, 0x6B, 0x6C, 0x6D, 0x6E, 0x6E,
0x70, 0x70, 0x72, 0x73, 0x74, 0x75, 0x77, 0x77, 0x78, 0x79, 0x7B, 0x7B, 0x7D, 0x7D, 0x7F, 0x7F, 0x81, 0x81, 0x83, 0x83, 0x8C, 0x8D, 0x8E, 0x8F, 0x88, 0x89, 0x8A, 0x8B, 0x8C, 0x8D, 0x8E, 0x87, 0x98, 0x91, 0x92, 0x93, 0x94, 0x95, 0x96, 0x97, 0x98, 0x99, 0x9A, 0x9A, 0x9C, 0x9C, 0x9E, 0x9E, 0xA0, 0xA0, 0xA2, 0xA2, 0xA4, 0xA4, 0xA6, 0xA6, 0xA8, 0xA8, 0xAA, 0xAA, 0xAC, 0xAC, 0xAE, 0xAE, 0xB0, 0xB1, 0xB2, 0xB3
};
int input = 0;
int i, j;
for ( input = 0; input < 0x10000 ; input++ )
{
int v10 = 0;
int v9 = 0;
int v6[30] = { 0 };
int count = 8;
while ( count )
{
--count;
for ( j = 22; j; v6[j] |= v10 << count )
{
v9 = data[22 * count + --j];
v10 = (v9 >> ((input >> (2 * count)) & 3)) & 1;
}
}
if( v6[0] == 'S' && v6[1] == 'U' && v6[2] == 'C' && v6[3] == 'T' && v6[4] == 'F' && v6[5] == '{' && v6[21] == '}')
{
for ( j = 0; j < 22; j++)
printf("%c", v6[j]);
}
}
return 0;
}
|